Process Dump is a Windows reverse-engineering tool to dump malware memory components back to disk for analysis. It uses an aggressive import reconstruction approach to make analysis easier, and supports 32 and 64 bit modules. Dumping of regions without PE headers is supported and in these cases PE headers and import tables will automatically be generated. Process Dump supports creation and use of a clean-hash database, so that dumping of clean files such as kernel32.dll can be skipped.
Process Dump comes in .zip format and supports Windows x86 and x64:
- Download: pd.exe v2.1.1 for Windows 32 and 64 bit
Process Dump: Dump memory modules to disk
Source Code
The source code for Process Dump is available through GitHub. Contributions are welcome:
- https://github.com/glmcdona/Process-Dump
- https://github.com/glmcdona/Process-Dump
Example Usage
Dump all modules from all processes (ignoring known clean modules):
- pd.exe -system
Dump all modules from a specific process identifier:
- pd.exe -pid 0x18A
Dump all modules by process name:
- pd.exe -p .*chrome.*
Build clean-hash database. These hashes will be used to exclude modules from dumping with the above commands:
- pd.exe -db gen
Run Process Dump in monitoring mode, dumping any process just before it closes:
- pd.exe -closemon
Dump code from a specific address in PID 0x1a3:
- pd.exe -pid 0x1a3 -a 0xffb4000
Generates two files (32 and 64 bit) that can be loaded for analysis in IDA with generated PE headers and
generated import table:
notepad_exe_x64_hidden_FFB40000.exe
notepad_exe_x86_hidden_FFB40000.exe
- pd.exe -system
Dump all modules from a specific process identifier:
- pd.exe -pid 0x18A
Dump all modules by process name:
- pd.exe -p .*chrome.*
Build clean-hash database. These hashes will be used to exclude modules from dumping with the above commands:
- pd.exe -db gen
Run Process Dump in monitoring mode, dumping any process just before it closes:
- pd.exe -closemon
Dump code from a specific address in PID 0x1a3:
- pd.exe -pid 0x1a3 -a 0xffb4000
Generates two files (32 and 64 bit) that can be loaded for analysis in IDA with generated PE headers and
generated import table:
notepad_exe_x64_hidden_FFB40000.exe
notepad_exe_x86_hidden_FFB40000.exe
Screenshots
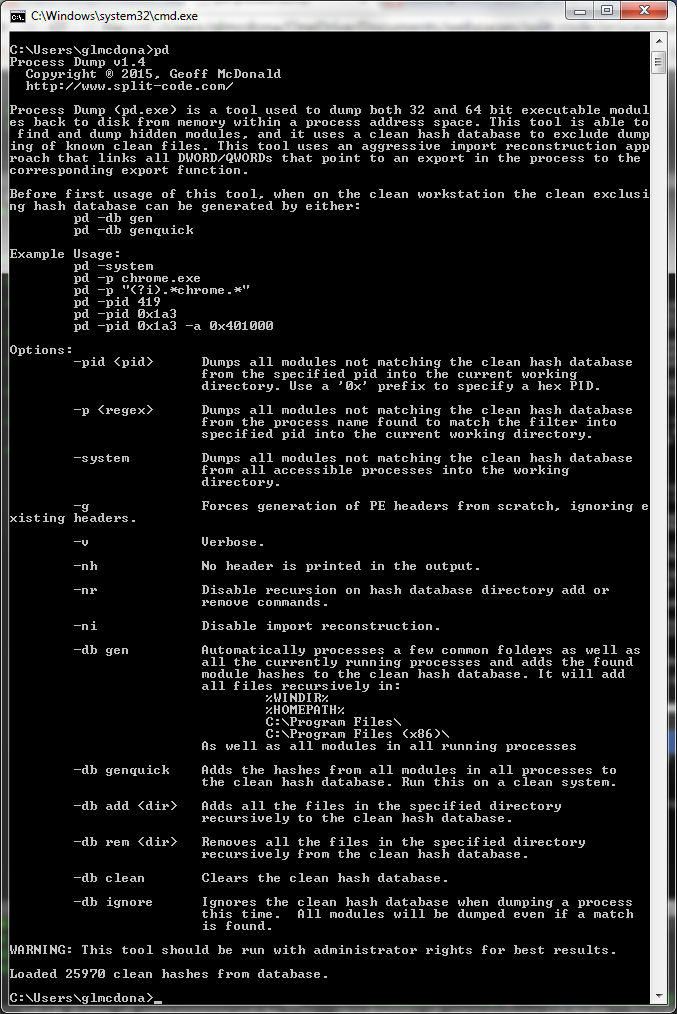
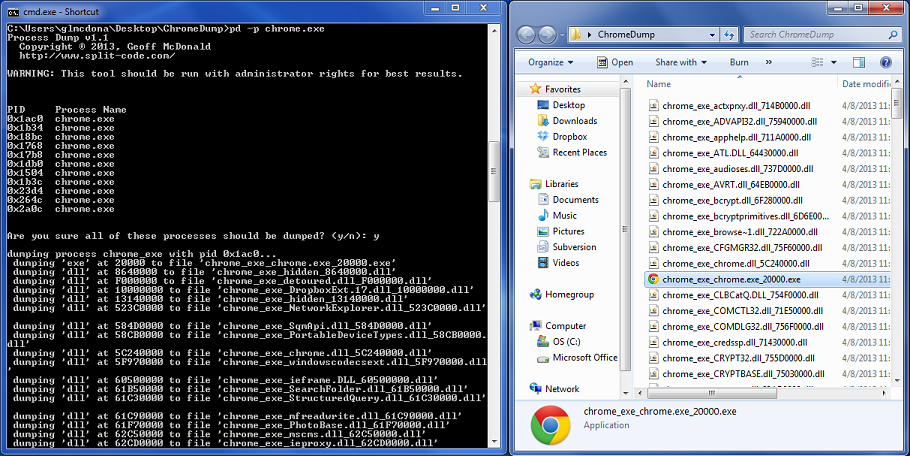
Full Help Page
Process Dump v2.1
Copyright ┬® 2017, Geoff McDonald
https://www.split-code.com/
https://github.com/glmcdona/Process-Dump
Process Dump (pd.exe) is a tool used to dump both 32 and 64 bit executable modules back to disk from memory within a process address space. This tool is able to find and dump hidden modules as well as loose executable code chunks, and it uses a clean hash database to exclude dumping of known clean files. This tool uses an aggressive import reconstruction approach that links all DWORD/QWORDs that point to an export in the process to the corresponding export function. Process dump can be used to dump all unknown code from memory ('-system' flag), dump specific processes, or run in a monitoring mode that dumps all processes just before they terminate.
Before first usage of this tool, when on the clean workstation the clean exclusing hash database can be generated by either:
pd -db gen
pd -db genquick
Example Usage:
pd -system
pd -pid 419
pd -pid 0x1a3
pd -pid 0x1a3 -a 0x401000 -o c:\dump\ -c c:\dump\test\clean.db
pd -p chrome.exe
pd -p "(?i).*chrome.*"
pd -closemon
Options:
-system Dumps all modules not matching the clean hash database
from all accessible processes into the working
directory.
-pid Dumps all modules not matching the clean hash database
from the specified pid into the current working
directory. Use a '0x' prefix to specify a hex PID.
-closemon Runs in monitor mode. When any processes are terminating
process dump will first dump the process.
-p Dumps all modules not matching the clean hash database
from the process name found to match the filter into
specified pid into the current working directory.
-g Forces generation of PE headers from scratch, ignoring existing headers.
-o Sets the default output root folder for dumped components.
-v Verbose.
-nh No header is printed in the output.
-nr Disable recursion on hash database directory add or
remove commands.
-ni Disable import reconstruction.
-nc Disable dumping of loose code regions.
-nt Disable multithreading.
-t Sets the number of threads to use (default 16).
-c Full filepath to the clean hash database to use for this run.
-db gen Automatically processes a few common folders as well as
all the currently running processes and adds the found
module hashes to the clean hash database. It will add
all files recursively in:
%WINDIR%
%HOMEPATH%
C:\Program Files\
C:\Program Files (x86)\
As well as all modules in all running processes
-db genquick Adds the hashes from all modules in all processes to
the clean hash database. Run this on a clean system.
-db add Adds all the files in the specified directory
recursively to the clean hash database.
-db rem Removes all the files in the specified directory
recursively from the clean hash database.
-db clean Clears the clean hash database.
-db ignore Ignores the clean hash database when dumping a process
this time. All modules will be dumped even if a match
is found.
Version History
Version 2.1.1 (January 24, 2022)
- Statically link libraries, which removes the pre-install dependency on Microsoft Visual C++ Redistributable per suggestion from Blaine for easier integration to Mandiant FLARE-VM (https://github.com/mandiant/flare-vm).
Version 2.1 (February 12th, 2017)
- Fixed a bug where the last section in some cases would instead be filled with zeros. Thanks to megastupidmonkey for reporting this issue.
- Fixed a bug where 64-bit base addresses would be truncated to a 32-bit address. It now properly keeps the full 64-bit module base address. Thanks to megastupidmonkey for reporting this issue.
- Addressed an issue where the processes dump close monitor would crash csrss.exe.
- Stopped Process Dump from hooking it's own process in close monitor mode.
Version 2.0 (September 18th, 2016)
- Added new flag '-closemon' which runs Process Dump in a monitoring mode. It will pause and dump any process just as it closes. This is designed to work well with malware analysis sandboxes, to be sure to dump malware from memory before the malicious process closes.
- Upgraded Process Dump to be multi-threaded. Commands that dump or get hashes from multiple processes will run separate threads per operation. Default number of threads is 16, which speeds up the general Process Dump dumping processing significantly.
- Upgraded Process Dump to dump unattached code chunks found in memory. These are identified as executable regions in memory which are not attached to a module and do not have a PE header. It also requires that the codechunk refer to at least 2 imports to be considered valid in order to reduce noise. When dumped, a PE header is recreated along with an import table. Code chunks are fully supported by the clean hash database.
- Added flags to control the filepath to the clean hash database as well as the output folder for dumped files.
- Fix to generating clean hash database from user path that was causing a crash.
- Fix to the flag '-g' that forces generation of PE headers. Before even if this flag was set, system dumps (-system), would ignore this flag when dumping a process.
- Various performance improvements.
- Upgraded project to VS2015.
Version 1.5 (November 21, 2015)
- Fixed bug where very large memory regions would cause Process Dump to hang.
- Fixed bug where some modules at high addresses would not be found under 64-bit Windows.
- More debug information now outputted under Verbose mode.
Version 1.4 (April 18, 2015)
- Added new aggressive import reconstruction approach. Now patches up all DWORDs and QWORDs in the module to the corresponding export match.
- Added '-a (address to dump)' flag to dump a specific address. It will generate PE headers and build an import table for the address.
- Added '-ni' flag to skip new import reconstruction algorithm.
- Added '-g' flag to force generation of new PE header even if there exists one when dumping a module. This is good if the PE header is malformed for example.
- Various bug fixes.
Version 1.3 (October 10, 2013)
- Improved handling of PE headers with sections that specify invalid virtual sizes and addresses.
- Better module dumping methodology for dumping virtual sections down to disk sections.
Version 1.1 (April 8, 2013)
- Fixed a compatibility issue with Windows XP.
- Corrected bug where process dump would print it is dumping a module but not actually dump it.
- Implemented the '-pid' dump flag.
Version 1.0 (April 2, 2013)
- Initial release.
- Statically link libraries, which removes the pre-install dependency on Microsoft Visual C++ Redistributable per suggestion from Blaine for easier integration to Mandiant FLARE-VM (https://github.com/mandiant/flare-vm).
Version 2.1 (February 12th, 2017)
- Fixed a bug where the last section in some cases would instead be filled with zeros. Thanks to megastupidmonkey for reporting this issue.
- Fixed a bug where 64-bit base addresses would be truncated to a 32-bit address. It now properly keeps the full 64-bit module base address. Thanks to megastupidmonkey for reporting this issue.
- Addressed an issue where the processes dump close monitor would crash csrss.exe.
- Stopped Process Dump from hooking it's own process in close monitor mode.
Version 2.0 (September 18th, 2016)
- Added new flag '-closemon' which runs Process Dump in a monitoring mode. It will pause and dump any process just as it closes. This is designed to work well with malware analysis sandboxes, to be sure to dump malware from memory before the malicious process closes.
- Upgraded Process Dump to be multi-threaded. Commands that dump or get hashes from multiple processes will run separate threads per operation. Default number of threads is 16, which speeds up the general Process Dump dumping processing significantly.
- Upgraded Process Dump to dump unattached code chunks found in memory. These are identified as executable regions in memory which are not attached to a module and do not have a PE header. It also requires that the codechunk refer to at least 2 imports to be considered valid in order to reduce noise. When dumped, a PE header is recreated along with an import table. Code chunks are fully supported by the clean hash database.
- Added flags to control the filepath to the clean hash database as well as the output folder for dumped files.
- Fix to generating clean hash database from user path that was causing a crash.
- Fix to the flag '-g' that forces generation of PE headers. Before even if this flag was set, system dumps (-system), would ignore this flag when dumping a process.
- Various performance improvements.
- Upgraded project to VS2015.
Version 1.5 (November 21, 2015)
- Fixed bug where very large memory regions would cause Process Dump to hang.
- Fixed bug where some modules at high addresses would not be found under 64-bit Windows.
- More debug information now outputted under Verbose mode.
Version 1.4 (April 18, 2015)
- Added new aggressive import reconstruction approach. Now patches up all DWORDs and QWORDs in the module to the corresponding export match.
- Added '-a (address to dump)' flag to dump a specific address. It will generate PE headers and build an import table for the address.
- Added '-ni' flag to skip new import reconstruction algorithm.
- Added '-g' flag to force generation of new PE header even if there exists one when dumping a module. This is good if the PE header is malformed for example.
- Various bug fixes.
Version 1.3 (October 10, 2013)
- Improved handling of PE headers with sections that specify invalid virtual sizes and addresses.
- Better module dumping methodology for dumping virtual sections down to disk sections.
Version 1.1 (April 8, 2013)
- Fixed a compatibility issue with Windows XP.
- Corrected bug where process dump would print it is dumping a module but not actually dump it.
- Implemented the '-pid
Version 1.0 (April 2, 2013)
- Initial release.